Serious vulnerabilities fixed in Omron CX-Supervisor
The vulnerabilities allow for denial of service and code execution with application privileges.
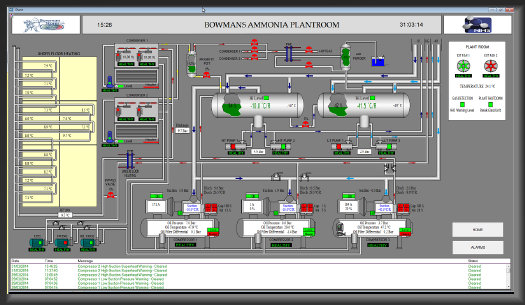
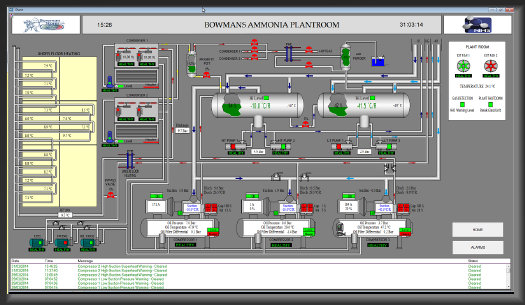
Japanese electronics manufacturer Omron has released an update for its CX-Supervisor software. The update fixes several vulnerabilities that could allow denial of service and code execution with application privileges. CX-Supervisor is software for creating human-machine interfaces for SCADA systems. The tool is used at enterprises worldwide, primarily in the energy sector.
Vulnerabilities in CX-Supervisor were discovered by security researcher Esteban Ruiz of Source Incite. The issues affect CX-Supervisor versions 3.42 and earlier, so users are strongly advised to update to the latest version 3.5.0.11.
CVE-2018-19011: An application can execute code embedded in a project file, allowing an attacker to execute malicious code within the context of the application. This vulnerability has a CVSS v3 score of 7.3 out of a maximum of 10.
CVE-2018-19013: An attacker can inject file deletion commands and/or delete the contents of files on a device by sending a specially crafted project file. This vulnerability has a CVSS v3 score of 5.0 out of a maximum of 10.
CVE-2018-19015: An attacker can inject commands to launch programs, as well as create, write, and read files on the device by sending a specially crafted project file. This vulnerability allows for code execution with application privileges. According to the CVSS v3 scoring system, this vulnerability has a score of 7.3 out of a maximum of 10.
CVE-2018-19017: Use-after-free vulnerability. When processing project files, the application fails to check whether they reference freed memory. Using a specially configured project file, an attacker can execute code with the application’s privileges. This vulnerability has a CVSS v3 score of 7.3 out of a maximum of 10.
CVE-2018-19019: A type confusion error occurs when the application processes project files. Using a specially crafted project file, an attacker can execute code with the application’s privileges. This vulnerability has a CVSS v3 score of 7.3 out of a maximum of 10.